Abstract
- Stingrays trick iPhones and Android gadgets alike into sharing delicate data, notably your IMSI quantity, which can be utilized for identification and monitoring.
- Android has non-compulsory protections like disabling 2G and blocking unencrypted communications, however help will depend on the precise cellphone you have got, and which model of Android it is operating.
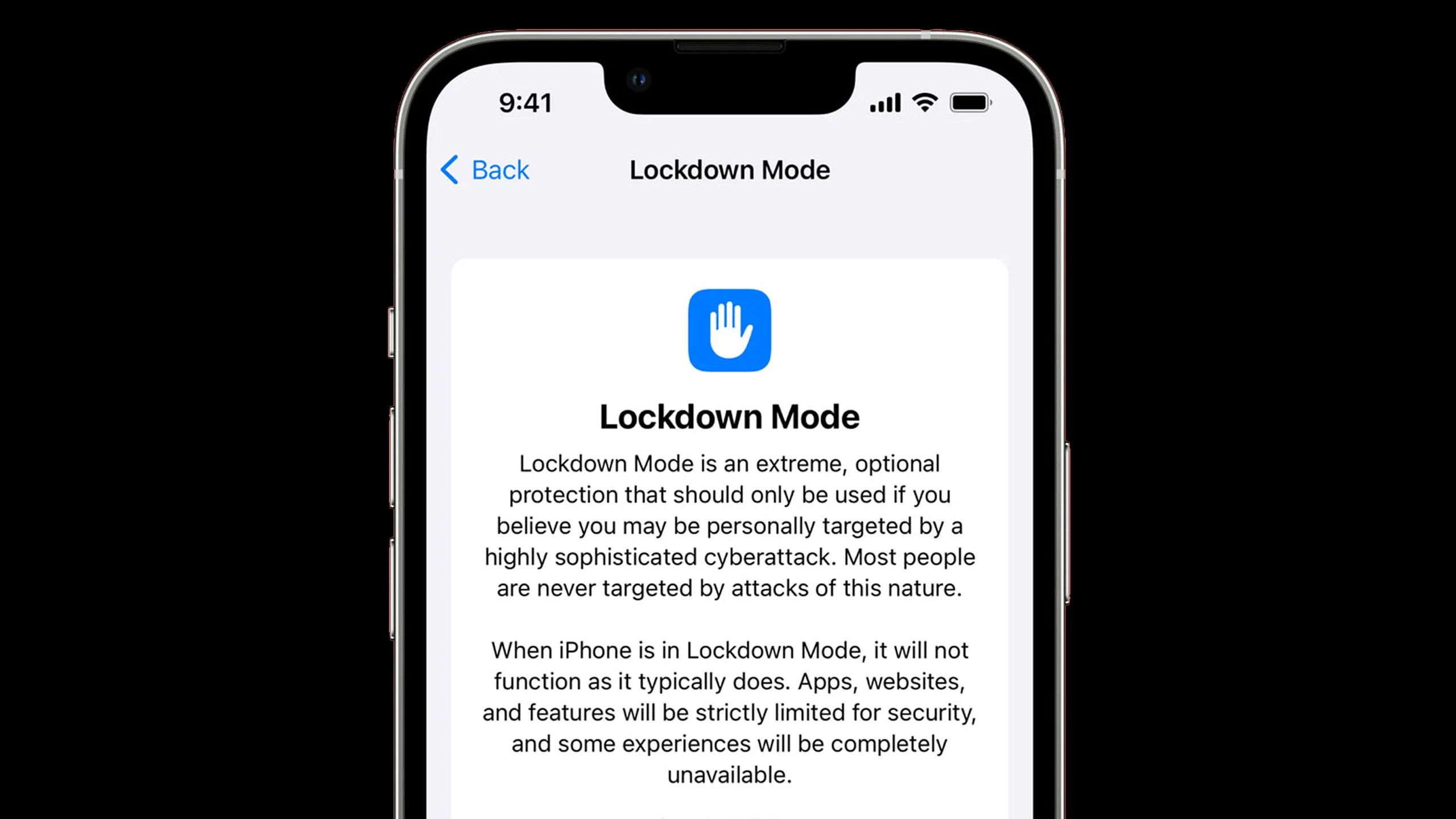
- iPhones have fewer defenses in opposition to stingrays except you allow Lockdown Mode.
It has been over a decade because the begin of the Snowden leaks, which uncovered mass surveillance packages within the US. I point out this as a result of one of many smaller issues Snowden (and others) drew consideration to is the usage of “stingrays,” often known as IMSI catchers. Police, navy, and intelligence companies have sometimes used these to intercept knowledge on cellphone customers with out their data — and criminals might now be making use of the expertise as nicely.
All this makes it clever to study a bit bit about how stingrays work, and how one can defend your iPhone or Android machine in opposition to them, since nobody has an inherent proper to intercept your cellphone site visitors and not using a warrant. What’s fascinating is that for the time being, Android 16 appears to supply a bonus on this space — although Apple will presumably catch up ultimately.
Associated
Do you really need to worry about spyware on your phone?
It is a matter of the place you reside, what you do, and what your safety habits are like.
What’s a stingray, and the way does it work?
Preying on hidden vulnerabilities
Unsplash
The very first thing to level out is that legally talking, the time period “stingray” derives from a particular product — the StingRay, made by the Harris Company. It is lots simpler to speak about stingrays than IMSI catchers, nevertheless, so the product grew to become a catch-all time period, a lot as some individuals check with all facial tissues as Kleenex.
Functionally, stingrays trick your cellphone into connecting to them by pretending to be a close-by mobile tower. As soon as that occurs, it is attainable to extract delicate knowledge, together with your cellphone’s IMSI (Worldwide Cell Subscriber Identification) quantity, which can be utilized to determine and observe you. Stingrays may additionally be used to gather metadata, and in some instances, the precise content material of communications. Extra hardly ever, stingrays are used as offensive weapons, say to conduct denial of service (DoS) assaults.
Any mobile machine inside vary of a stingray is prone to connecting to it, so your knowledge could also be snatched up even once you aren’t an supposed goal.
This will all sound like one thing your cellphone ought to have the ability to defend in opposition to, however stingrays can dupe your cellphone into utilizing a protocol with weaker safety, as an example by briefly switching you from 5G to 2G, which most carriers have deserted. Usually, automated hopping is an effective factor — it retains you linked as you progress between areas with completely different protection. But when it is not dealt with correctly, it could turn out to be an assault vector.
One of many terrifying issues about stingrays is that they are non-discriminatory. That’s, any mobile machine inside vary of a stingray is prone to connecting to it, so your knowledge could also be snatched up even once you aren’t an supposed goal. This and different points have drawn the eye of scrutiny of teams just like the American Civil Liberties Union and the Digital Frontier Basis. There’s extra to clarify than I can presumably go into right here, so I encourage you to study extra, notably should you’re planning to hitch a politically delicate protest.
defend an Android machine in opposition to stingrays
The most effective safety is reserved for the newest gadgets
An important factor is preserving Android up-to-date, and being conscious of its anti-stingray choices. If you happen to’ve bought Android 12 or later, you’ll be able to disable 2G connectivity fully by going to Settings -> Community & Web -> SIMs, selecting your SIM, then toggling off Permit 2G. Don’t fret — most cellphone carriers have switched completely to 4G and 5G, so you will not discover any calls, texts, or knowledge interrupted. Certainly even 3G networks are being deprecated, since they’re too gradual to maintain up with the calls for of contemporary apps.
Android 14 expands this safety with an possibility to dam “null ciphers,” i.e. unencrypted communications. There is not any professional motive to be utilizing unencrypted knowledge anymore, given how harmful the web could be, so disabling null ciphers is an apparent manner of mitigating the specter of stingray assaults. Android 15 takes yet one more step ahead, enabling a notification at any time when a community asks for distinctive machine identifiers, or forces weaker safety.
The one zero-risk possibility, although, is to dam mobile exercise completely.
Android 16 features a Cell community safety web page to centralize issues, which you need to have the ability to attain through Settings -> Safety & privateness -> Security Middle. There is a massive catch, nevertheless — it solely seems on gadgets with specific modems, and model 3.0 or later of Android’s IRadio {hardware} abstraction layer (HAL). You are unlikely to see the web page in any respect, even should you personal one thing as latest as a Pixel 9. You might have to attend on your subsequent cellphone improve to check this out.
The excellent news right here is that many Android telephones ought to help disabling 2G, no less than. It is simply much less handy and safe than what the newest and biggest Android 16 gadgets are able to.
If you happen to’re in a high-risk scenario, there are apps that may doubtlessly warn you about stingrays, equivalent to SnoopSnitch. The one zero-risk possibility, although, is to dam mobile exercise completely, and that applies to each iPhones and Android gadgets.

Associated
Is it safe to use Apple AirTags?
The dangers are normally very low, however you want to concentrate on them.
defend an iPhone in opposition to stingrays
Time to play catch-up
Apple
iPhones are lagging behind relating to stingray safety, however they don’t seem to be defenseless. You possibly can, for instance, go to Settings -> Mobile -> Mobile Information Choices -> Voice & Information and select both 5G On or LTE. The 5G Auto possibility does enhance battery life, however will increase your probabilities of being kicked right down to a much less safe community.
If you happen to use that step, you might also wish to go to Settings -> Mobile -> Community Choice and disable Computerized, however be warned — this feature can create havoc. Chances are you’ll end up unable to roam home networks, and you will have to manually choose a provider once you journey overseas. It is in all probability not well worth the trouble.
That is partly as a result of in iOS 16 or later, Apple affords a characteristic known as Lockdown Mode. This allows a large set of safety measures, largely supposed for journalists, dissidents, and others prone to being focused by authoritarian regimes or overseas governments. If you happen to’re really apprehensive about stingrays, although, Lockdown Mode forcibly disables 2G, and limits how your iPhone can work together with the skin world. It is so draconian that you need to keep away from it except completely mandatory — even many web sites and Messages attachments will not work.
It isn’t clear but whether or not iOS 26, coming fall 2025, will provide any enhancements to stingray safety. I am anticipating Apple to meet up with Android in some unspecified time in the future, nevertheless, because the firm prides itself on safety and privateness.

You may also like
Everything you need to know about PEVs, or personal electric vehicles
You should utilize PEVs like e-bikes and scooters to discover, run errands, or velocity up your commute.
Trending Merchandise